Cracking WPA2 with Hashcat
 Thursday, August 8, 2013 at 3:24PM
Thursday, August 8, 2013 at 3:24PM So for all those who got to see the show at Defcon's wireless village, that talk focused more on the drinking of the Rolling Rock than the cracking of the hashes.
I said in my ramblings that it was really really really easy.
Here is a how to... with some example files for you to follow along with.
First you want to capture some traffic. I leave the logistics of how up to you.
For this demo, we will be using a file which I grabbed online from the wireshark wiki.
http://wiki.wireshark.org/SampleCaptures?action=AttachFile&do=get&target=wpa-Induction.pcap
Now that you have some traffic in the form of a PCAP, fire up wireshark.
First thing I do is enter "eapol" in the search window. This confirms we have a handshake. You can skip this step if you really really want to but remember the whole trust but verify.
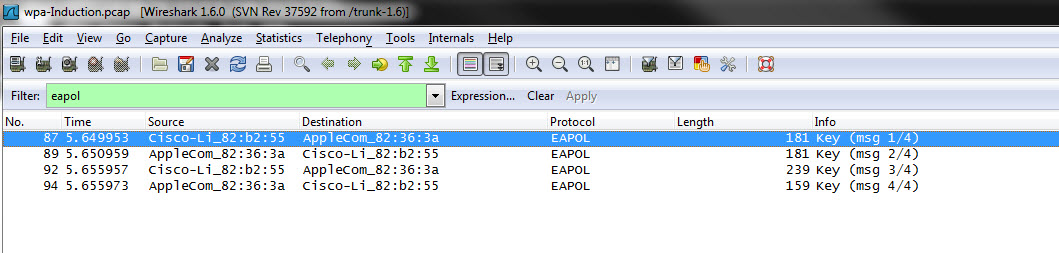
Since WPA/2 salts with the SSID, it can help to know what that is. Using the find menu in wireshark, search for the string SSID.
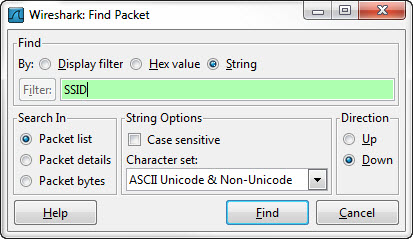

So the SSID is named "Coherer" which is good because at least it isn't Linksys.
Now here is the hardest part. You need to convert your pcap file to a hccap file. Hashcat has a cloud version of the tool which works awesome. You can run some command line tools as well but the point of the talk was to not use aircrack.
https://hashcat.net/cap2hccap/
In real life, we all use aircrack so you can use 2 different commands.
I have used this...
aircrack-ng <cap> -J <hccap>
This could work as well...
wpaclean <out> <in>
wpaclean can damage your file so backup if you want to give it a try.
Now you have your hccap file.
Download the latest version of oclHashcat from here.
Run this below:
cudaHashcat-plus64.exe --hash-type 2500 wpa.hccap dict.txt
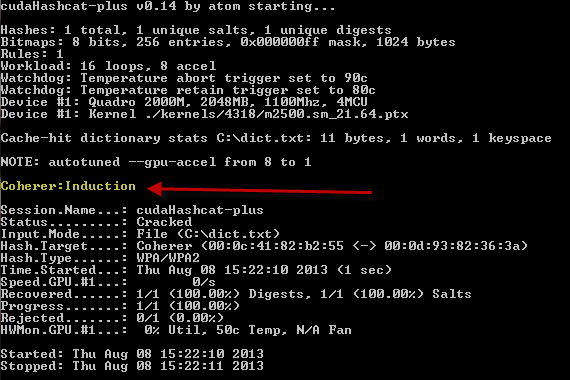
For the demo I used a dictionary with 1 word for demo speed but that word is in the rockyou list (entry 922007).
I use cudaHashcat-plus64.exe because I have a nVidia card as well as a 64 bit system. The base application may change but the flags are the same and the passwords are still weak.
Happy cracking!