Protected by (in)Security Tools
 Monday, September 19, 2011 at 5:51PM
Monday, September 19, 2011 at 5:51PM
I was at my local ISSA meeting listening to a vendor talk about their Security Device. The first part of the slide deck was the marketing piece. This device will protect you from all attacks, allow you to control your network and alert you to any shenanigans.
I really liked this tool but I believe it "trust but verify." He said that you could install an agent on every machine (meh) or you can use the new and improved agent less deployment option. Using remote procedure calls, the device would to authenticate to the machine and perform compliance checks against a pre-defined security policy. It would do this on a periodic basis.
Me: So the clairfy, the device uses a SINGLE log in to access EACH machine it enconters on the network.
Vendor: Yes, usually a domain admin account. We don't recommend using an Enterprise Admin account.
Me: No $hit, I don't recommend this either. So what about kidnapping the tokens?
Vendor: We don't log into the machine, we just run code on it.

Me: I can steal the token with incognito and I will have domain admin rights. Your "security tool" just compromised every machine on the network.
I explained it to one of the people in the room who use his product. I haven't heard back from him in a week because he is probably removing that garbage from all of his machines.
Today I saw a tweet taking about UNITED Summit and HD Moore's presentation.
RT @RealGeneKim: #UNITEDSummit: @hdmoore: pointing out that security tools often vector to shells, due to Windows auth mechanisms. Ouch
This is a problem with many tools in the marketplace. I do have to admit, until the gaping hole was noted, I did like the product. Hopefully they get 2.0 out soon!
 incognito,
incognito,  insecurity tools in
insecurity tools in  Hacking
Hacking Hacking a Hurricane
 Tuesday, August 30, 2011 at 11:19AM
Tuesday, August 30, 2011 at 11:19AM As my friends in the Northeast will attest to, Hurricanes don't just suck. They blow! Food markets are picked dry, Home Depot sells out of wood, and who can forget the pleasant experience of the gas station.
That pleasant experience is the focus today.
Filling up with gas before or after a storm is a riot waiting to happen. The lines are longer than the Toy Story Ride at Disney's Hollywood Studios. (I have a hack for that as well but that is a different blog post.)
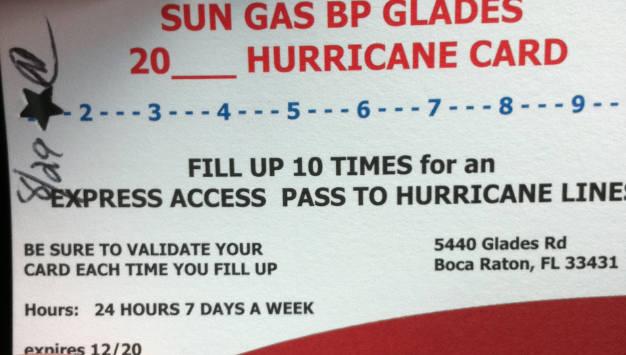
Today when I filled up my car at the gas station I saw this.
Front:
 Back:
Back:
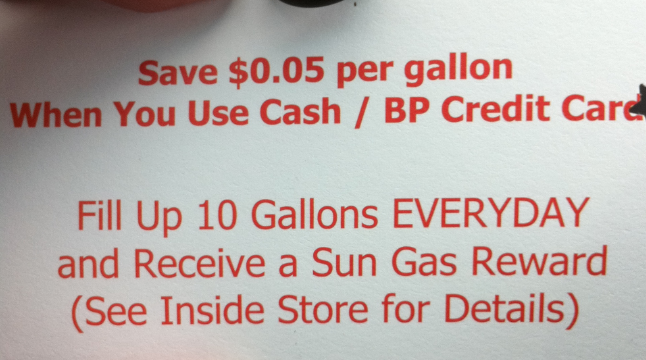
This BP gas station is offering you a chance to skip the lines (no word on offering protection from your pissed off neighbors) and fill up with gas sans the waiting. Tom Petty said it best, "The Waiting is the hardest part!" Go Gators!
I am reading Kevin Mitnick's book, Ghost in the Wires. Kevin's earliest hacks was figuring out that he could ride the bus for free by taking a used transfer ticket and punching it himself.
Lets look at the controls associated with this "promotion."
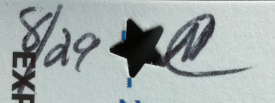
A star punched out along with the date and a "impossible to forge" signature.
I asked someone at work where I could get a hole punch. She offered to let me borrow her set. Hearts, Stars, Clovers, and every other shape that was in a box of Lucky Charms. How magically Delicious!
So I went back to the store after punching all 10 spots in the extra card I liberated from the stack on the counter and I was able to redeem it for a permanent card entitling me to skip the line and fill up 1 car and 2 gas canisters. I believe in a ruling class because I rule!
Remember, there is a difference between old tricks and classic ones!
(I also did not blot out the address of the gas station for all my local hackers. Use this trick well but remember, Snitches get Stitches!)
Malware Removal Guide
 Thursday, August 25, 2011 at 10:13AM
Thursday, August 25, 2011 at 10:13AM I recently came across an awesome site that I wanted to share. This site is ran by an awesome guy named Brain. You can follow him on twitter at @realsecurity.
His site has some EXCELLENT malware information.
Among the content is
- A listing of Malicious IP Addresses and Malware Block Lists. For my malware research friends it is a couple of great leads. :)
- List of Online AV/AntiMalware scanners
- Automated Malware Analysis Services
- Resources for Personal Computer Security
- Network Security
- Web Security
- Security Checklists
Among the treasures found at this site, Brain has a one of the most detailed malware removal guide for Windows that I have seen.
Bookmark this site.
 Awesome Sites in
Awesome Sites in  Virus/Malware
Virus/Malware 
