Social Engineering using Metasploit Express
 Wednesday, September 15, 2010 at 2:37PM
Wednesday, September 15, 2010 at 2:37PM In honor of the release of the findings from Defcon 18 Social Engineering CTF ‐ "How Strong Is Your Schmooze” as well as the weekly update from Metasploit Express I will walk through a Social Engineering attack using Metasploit Express.
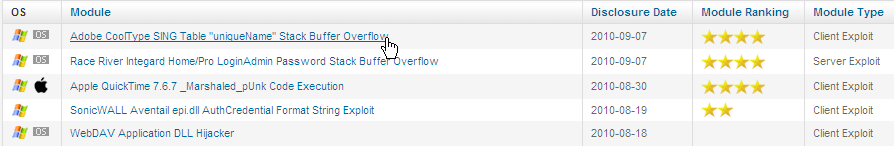
Step 1: Under Modules, pick your exploit. I am using the Adobe CoolType SING exploit. (We don't want to leave out Windows Vista and Windows 7.)
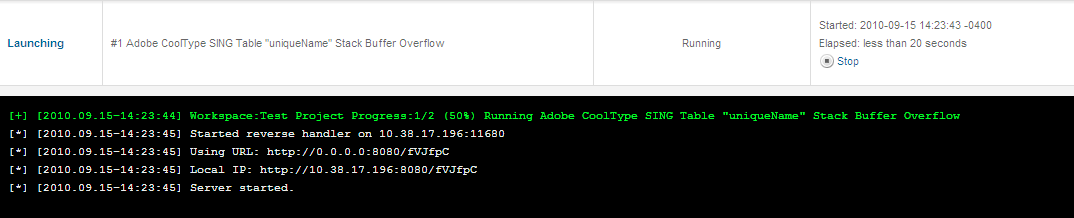
Step 2: Leave every option as the default and launch the attack.
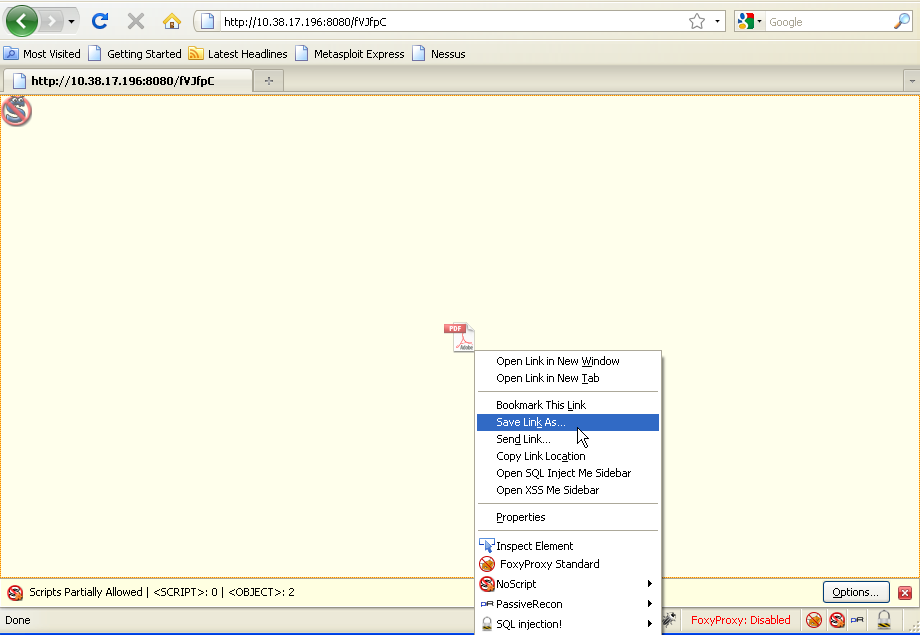
Step 3: We could just have our target browse to the web address however we are going to use a different attack vector. Go and Find a USB drive and load up FireFox with NoScript enabled. Browse to the target URL and save the PDF. NoScript will stop it from executing on your machine.
Step 4: Rename the file something sneaky. I chose HR.pdf. Copy this to your thumb drive.

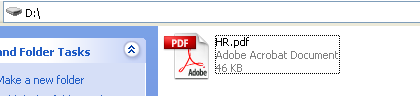
Step 5: Take your USB Drive and drop it off somewhere.

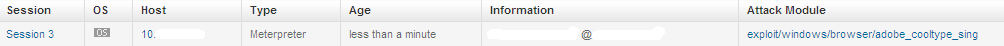
Step 6: Wait for the finder of the USB drive to open and click the evil HR.pdf. Gotcha! Time to give Mr. X a lesson on Social Engineering and how we don't use thumb drives we find in the bathroom.

 Metasploit Express,
Metasploit Express,  adobe in
adobe in  Hacking
Hacking 
Reader Comments (2)
I have been really glad after reading this blog as the knowledge which has been given via this blog is simply tremendous. I would congratulate and appreciate the blogger for doing this much hard work.
Thanks